Hackers Use Twitter, Memes, And Hidden Instructions In New Hack
By: Jim Stickley and Tina Davis
January 28, 2019
 It’s the latest and one of the sneakiest social media hacks using Twitter as the conduit. Security researchers recently found a new kind of malware hiding in plain sight. It involves memes sent via Twitter, although the memes themselves aren’t infected. They are merely the messengers. It’s a roundabout way for hackers to get more information from devices that were already infected with malware sent from the attackers. We know hackers are constantly reinventing themselves and their ways of stealing data. This particular hack is considered “creative” by security researchers and was discovered last last year. It also shows the lengths hackers will go to get your personal information.
It’s the latest and one of the sneakiest social media hacks using Twitter as the conduit. Security researchers recently found a new kind of malware hiding in plain sight. It involves memes sent via Twitter, although the memes themselves aren’t infected. They are merely the messengers. It’s a roundabout way for hackers to get more information from devices that were already infected with malware sent from the attackers. We know hackers are constantly reinventing themselves and their ways of stealing data. This particular hack is considered “creative” by security researchers and was discovered last last year. It also shows the lengths hackers will go to get your personal information.
The memes sent by hackers via Twitter contain code that directs the infected device to take screen shots of the screen. They connect to Twitter directly, making the attack less likely to be discovered. Then they use hidden code to direct actions. That hidden code is called steganography. Techopedia says, “Steganography is an encryption technique that can be used along with cryptography as an extra-secure method in which to protect data” and can be used in images as well as audio and video files. That’s how these memes are going undetected.
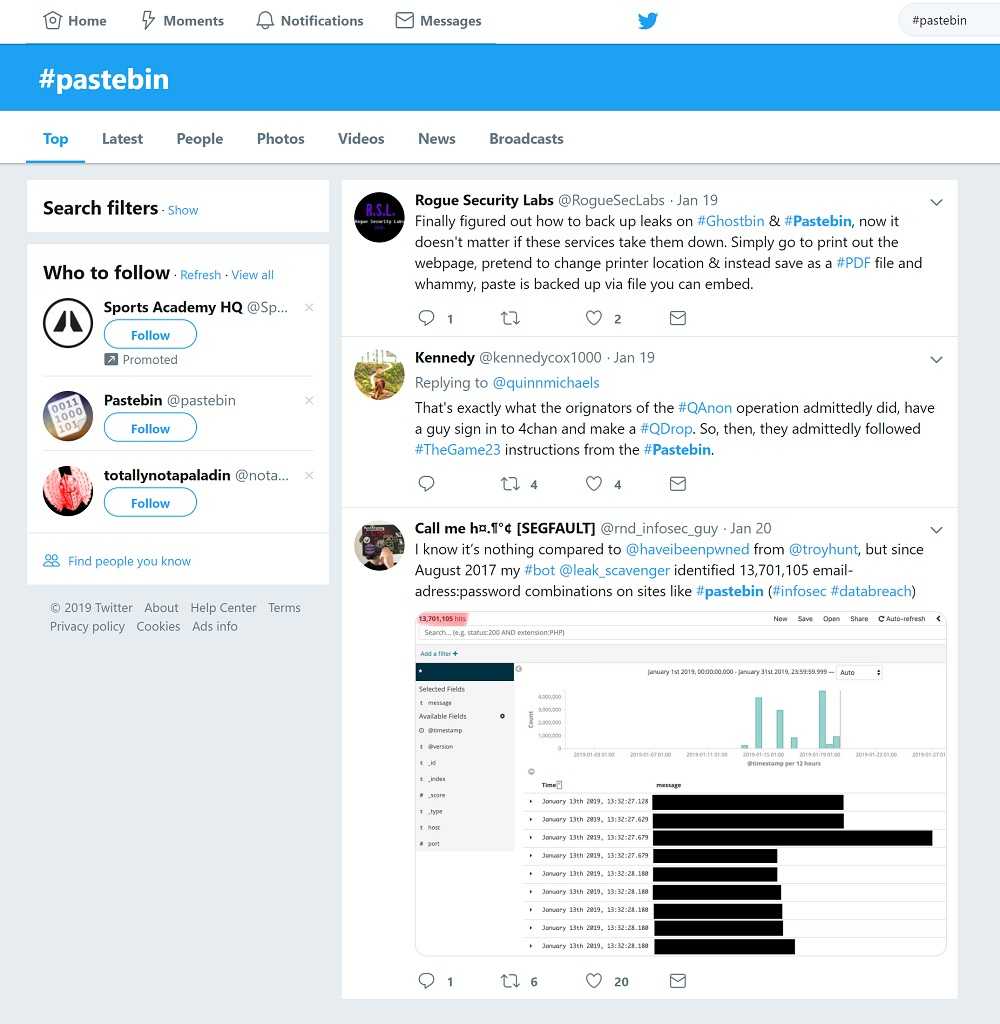
In this case, the data stored in the screen shots—the images--is then sent to one of thousands of Pastebin applications for storage, where it is encrypted and stored for later use by the hackers. This unique hack relies on steganography memes, Twitter, and Pastebins (online storage service). It’s a process, but it’s a process that works. We’re now seeing ever more creative and patient hackers that are willing to use all kind of routes, including memes on Twitter, to steal and abuse your personal information.
Security researchers still have more work to do to understand this malware. It’s not known where it comes from or who is behind it. Still, others wonder if this is a proof-of-concept--a trial scenario to be used on a larger scale for a bigger purpose in the future.
 Keeping a device malware-free takes awareness by the owner, but simple steps to avoid downloading malware are the place to start. Whether at home or at work, there’s no shortage of phishing attacks by email, text, and voice. Webroot Threat Report finds that every month, nearly 1.5 million new phishing sites are created. Users should be suspicious any email out of the ordinary, and even those that appear harmless. Clicking an attachment in a phishing email can download malware on your device. Following a link contained in a phishing email can redirect users to a bogus website, no matter how legitimate it appears. These fake sites are designed to steal any information you put into them, like logins and account numbers. Teaching employees how to spot phishing emails and learning to spot them on your personal device can prevent a whole lot of damage and headaches.
Keeping a device malware-free takes awareness by the owner, but simple steps to avoid downloading malware are the place to start. Whether at home or at work, there’s no shortage of phishing attacks by email, text, and voice. Webroot Threat Report finds that every month, nearly 1.5 million new phishing sites are created. Users should be suspicious any email out of the ordinary, and even those that appear harmless. Clicking an attachment in a phishing email can download malware on your device. Following a link contained in a phishing email can redirect users to a bogus website, no matter how legitimate it appears. These fake sites are designed to steal any information you put into them, like logins and account numbers. Teaching employees how to spot phishing emails and learning to spot them on your personal device can prevent a whole lot of damage and headaches.