Even Cybercriminals Can Be Victims Of Their Own Weak Passwords
By: Jim Stickley and Tina Davis
August 8, 2017
Attention to everyone who still uses easy-to-guess passwords and phrases for online accounts. In a presentation to Black Hat attendees this year, Department of Justice (DOJ) officials discussed how they took down a Russian cybercriminal in 2014. No, they didn’t trace his activity or bug his home. It was not nearly so sophisticated. It wasn’t even a technical solution. They merely guessed the password that he used to lock his computer.
 That’s right. They guessed it. It wasn’t so simple as the ever-popular “123456,” but by finding out he referenced a particular phrase in his email dialogue often, they combined that word with “123” and shockingly, it worked.
That’s right. They guessed it. It wasn’t so simple as the ever-popular “123456,” but by finding out he referenced a particular phrase in his email dialogue often, they combined that word with “123” and shockingly, it worked.
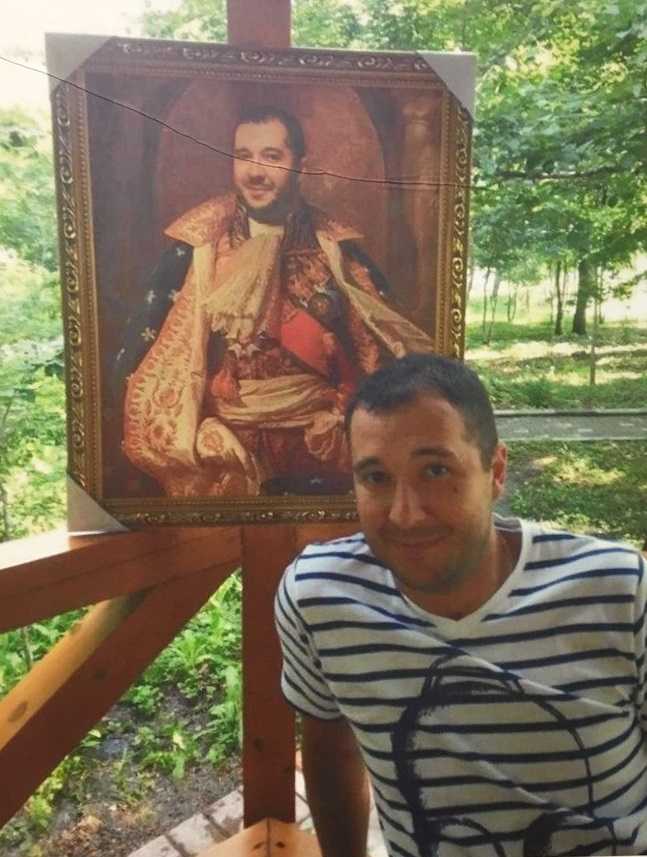
Once on Roman Seleznev’s computer, they found 1.7 million stolen credit card numbers and webpages that explained how to use the stolen numbers. To make it even more unbelievable, the files weren’t even encrypted.
 When choosing passwords and phrases, put some effort into it. It’s understandable to want to use the same one for each account, but don’t. Password reuse still exists and is quite successful. If federal authorities can merely guess a password of an infamous cybercriminal, those cybercriminals are likely to reuse yours if they steal it. They may get lucky too. Use unique ones for all accounts. If you must write them down, do so. Just keep it on a list separate from your devices. If possible, use clues instead of the actual passwords.
When choosing passwords and phrases, put some effort into it. It’s understandable to want to use the same one for each account, but don’t. Password reuse still exists and is quite successful. If federal authorities can merely guess a password of an infamous cybercriminal, those cybercriminals are likely to reuse yours if they steal it. They may get lucky too. Use unique ones for all accounts. If you must write them down, do so. Just keep it on a list separate from your devices. If possible, use clues instead of the actual passwords.
 Always use a minimum of eight characters including upper and lower case letters, numbers, and special characters. Mix up the locations of the numbers and special characters too. There have been studies showing that the vast majority of the time, those are at the end of passwords. It is only a matter of time before hacking tools are developed that can easily determine that too.
Always use a minimum of eight characters including upper and lower case letters, numbers, and special characters. Mix up the locations of the numbers and special characters too. There have been studies showing that the vast majority of the time, those are at the end of passwords. It is only a matter of time before hacking tools are developed that can easily determine that too.
 Never use personally identifiable information (PII) in your passwords. PII includes birthdates, social security numbers, or driver’s license numbers, for example.
Never use personally identifiable information (PII) in your passwords. PII includes birthdates, social security numbers, or driver’s license numbers, for example.
Seleznev was sentenced to 27 years in prison for stealing payment card details from point of sale systems and selling it in the underground markets. According to the DOJ, he defrauded victims to the tune of more than $169 million.